Säkra er cybersäkerhet
Säkerställ cybersäkerheten. Vi hjälper er att skydda verksamheten, uppfylla NIS2-kraven och förbli säkra – utan komplexitet
NIS 2 Compliance
Cyberattacker ökar
Cyberattacker ökar
De flesta företag är inte tillräckligt förberedda
Cyberhygien
24/7 support
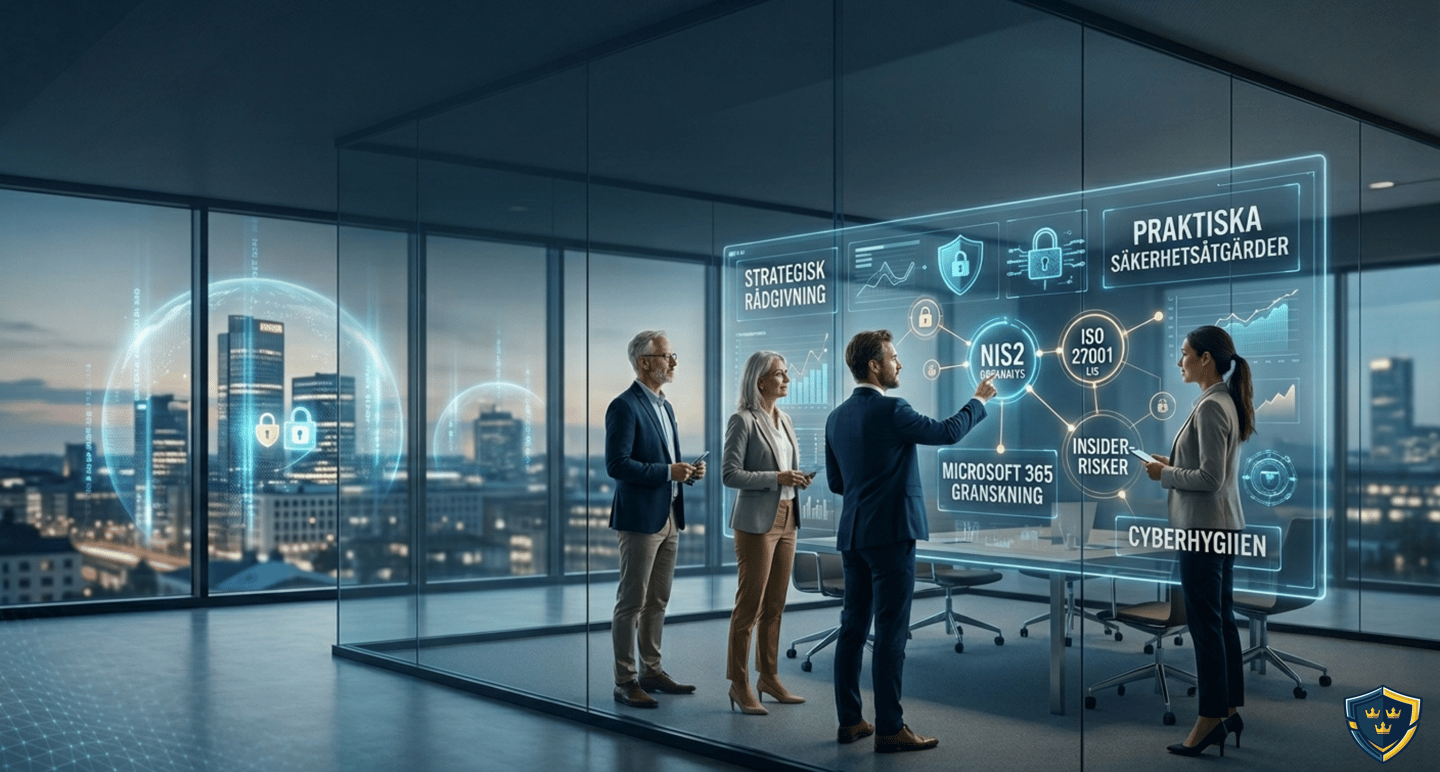
Helhetslösningar för din cybersäkerhet och regelefterlevnad
Vi hjälper er att navigera i ett komplext hotlandskap genom strategisk rådgivning och praktiska säkerhetsåtgärder. Från gapanalyser inför NIS2 och införande av ledningssystem enligt ISO 27001, till djuppgående säkerhetsgranskningar av Microsoft 365 och hantering av insider-risker. Med fokus på stark cyberhygien och optimering av era befintliga verktyg stärker vi er motståndskraft, minimerar sårbarheter och säkerställer att ni uppfyller alla lagkrav – snabbt, tydligt och utan onödig komplexitet

KONTAKT
TELEFON
contact@sweshield.se
+46 76 264 38 08
Sweshield behandlar personuppgifter i enlighet med EU:s dataskyddsförordning (GDPR) och tillämplig svensk lagstiftning. Vi arbetar kontinuerligt med tekniska och organisatoriska säkerhetsåtgärder för att skydda personuppgifter och affärsinformation.
Informationen på denna webbplats tillhandahålls endast i informationssyfte och utgör inte juridisk rådgivning.
© 2026 Sweshield. Alla rättigheter förbehållna.
Juridik & Dataskydd
